VPN(トンネル・エンドポイント・ディスカバリ 6)
「VPN(トンネル・エンドポイント・ディスカバリ 5)」の続きです。
ここでは、各ルータのコンフィグを紹介していきます。
※Router_B、Router_CのE0は、「no keepalive」コマンドで、強制的にUPさせます。
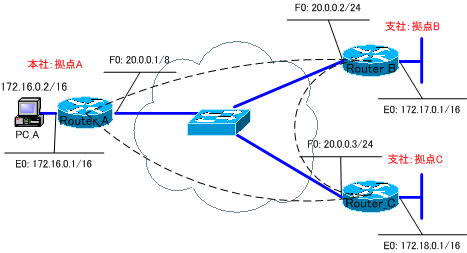
各ルータの設定は、以下のようになります。
●Router_Aの設定
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname Router_A
!
boot-start-marker
boot-end-marker
!
enable password cisco
!
no aaa new-model
memory-size iomem 25
!
ip cef
!
crypto isakmp policy 1
authentication pre-share
crypto isakmp key cisco address 0.0.0.0 0.0.0.0
!
crypto ipsec transform-set TS-IPSEC esp-3des esp-sha-hmac
!
crypto dynamic-map MAP-IPSEC 1
set transform-set TS-IPSEC
match address 100
crypto dynamic-map MAP-IPSEC 2
set transform-set TS-IPSEC
match address 101
!
crypto map TEDTAG 1 ipsec-isakmp dynamic MAP-IPSEC discover
!
interface Ethernet0
ip address 172.16.0.1 255.255.0.0
half-duplex
!
interface FastEthernet0
ip address 20.0.0.1 255.0.0.0
speed auto
crypto map TEDTAG
!
ip forward-protocol nd
ip route 172.17.0.0 255.255.0.0 20.0.0.2
ip route 172.18.0.0 255.255.0.0 20.0.0.3
no ip http server
no ip http secure-server
!
access-list 100 permit ip 172.16.0.0 0.0.255.255 172.17.0.0 0.0.255.255
access-list 101 permit ip 172.16.0.0 0.0.255.255 172.18.0.0 0.0.255.255
!
control-plane
!
line con 0
line aux 0
line vty 0 4
password cisco
login
!
end
●Router_Bの設定
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname Router_B
!
boot-start-marker
boot-end-marker
!
enable password cisco
!
no aaa new-model
memory-size iomem 25
!
ip cef
!
crypto isakmp policy 1
authentication pre-share
crypto isakmp key cisco address 0.0.0.0 0.0.0.0
!
crypto ipsec transform-set TS-IPSEC esp-3des esp-sha-hmac
!
crypto dynamic-map MAP-IPSEC 1
set transform-set TS-IPSEC
match address 100
crypto dynamic-map MAP-IPSEC 2
set transform-set TS-IPSEC
match address 101
!
crypto map TEDTAG 1 ipsec-isakmp dynamic MAP-IPSEC discover
!
interface Ethernet0
ip address 172.17.0.1 255.255.0.0
half-duplex
no keepalive
!
interface FastEthernet0
ip address 20.0.0.2 255.0.0.0
speed auto
crypto map TEDTAG
!
ip forward-protocol nd
ip route 172.16.0.0 255.255.0.0 20.0.0.1
ip route 172.18.0.0 255.255.0.0 20.0.0.3
no ip http server
no ip http secure-server
!
access-list 100 permit ip 172.17.0.0 0.0.255.255 172.16.0.0 0.0.255.255
access-list 101 permit ip 172.17.0.0 0.0.255.255 172.18.0.0 0.0.255.255
!
control-plane
!
line con 0
line aux 0
line vty 0 4
password cisco
login
!
end
●Router_Cの設定
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname Router_C
!
boot-start-marker
boot-end-marker
!
enable password cisco
!
no aaa new-model
memory-size iomem 25
!
ip cef
!
crypto isakmp policy 1
authentication pre-share
crypto isakmp key cisco address 0.0.0.0 0.0.0.0
!
crypto ipsec transform-set TS-IPSEC esp-3des esp-sha-hmac
!
crypto dynamic-map MAP-IPSEC 1
set transform-set TS-IPSEC
match address 100
crypto dynamic-map MAP-IPSEC 2
set transform-set TS-IPSEC
match address 101
!
crypto map TEDTAG 1 ipsec-isakmp dynamic MAP-IPSEC discover
!
interface Ethernet0
ip address 172.18.0.1 255.255.0.0
half-duplex
no keepalive
!
interface FastEthernet0
ip address 20.0.0.3 255.0.0.0
speed auto
crypto map TEDTAG
!
ip forward-protocol nd
ip route 172.16.0.0 255.255.0.0 20.0.0.1
ip route 172.17.0.0 255.255.0.0 20.0.0.2
no ip http server
no ip http secure-server
!
access-list 100 permit ip 172.18.0.0 0.0.255.255 172.16.0.0 0.0.255.255
access-list 101 permit ip 172.18.0.0 0.0.255.255 172.17.0.0 0.0.255.255
!
control-plane
!
line con 0
line aux 0
line vty 0 4
password cisco
login
!
end
続きは、次の「VPN(トンネル・エンドポイント・ディスカバリ 7)」で、設定した3拠点によるTEDの構成を検証していきます。